For a short summary of what we’ve used before, I suggest looking at the first post in this topic (it’s outdated, but mostly correct for the beginning), and the wiki (even though it’s a bit of a mess right now).
Other than that: not much real programming has been done, as in, so far we have not written any programs by hand (as far as I know), except implementations of encryption algorithms that did not seem to be the answer.
What we have done is use pre-made tools. Some of these tools (for windows at least) include:
[list][*]ASCII85 decoder (used to decode the HALOS.txt file, resulting in the 752 hex code)
-
Online decryption tool (used to decrypt information using common algorithms, see also Cryptool below)
[/:m][]Cryptool (used to encrypt and decrypt information using common algorithms)[/:m]
[]Sonic Visualiser and similar (used to visualise sound files, as they can potentially contain patterns or information graphically)[/:m]
[]MMSSTV or RX-SSTV (used to decode SSTV images, an ancient image-through-sound protocol used by amateur radio operators - for more info, wikipedia is your friend)[/:m]
[]HxD and other hex editors (used to look for data us humans can understand within hex files)[/:m]
[]Photoshop (sorry, no link there) and similar image manipulation software, perhaps Paint.NET or GIMP? (used to mess around with images, levels in particular as it can sometimes reveal hidden data)[/*:m][/list:u]Other tools may have been used but these are the main ones that come to mind.
As for codes / ciphers / encodings used: several so far, actually. These include:
One more thing: Stormseeker, the guy behind the ARG, has dropped various hints regarding the code / cipher / encryption progression. In particular, he wrote this in a PM to @Gunsrequiem a long time ago. Now, clearly, as it was not yet known at the time he was actually stormseeker, he was pretending to not know exactly what was going on. As such, he may have intentionally given some misinformation to keep us from suspecting anything, or keep us busy. As he said, “[the HALOS.txt file] is a holding puzzle, designed to allow time to construct further aspects of the ARG or work on whatever is behind their NDA”. Still, it’s unlikely he intentionally set us on a trail of red herrings with no valid information somewhere in there, and it’s pretty much the only thing we’ve got to hold on to right now… except his recent remarks on the steam release stream. (For a transcript and some analysis, check out this post I made a while back.)
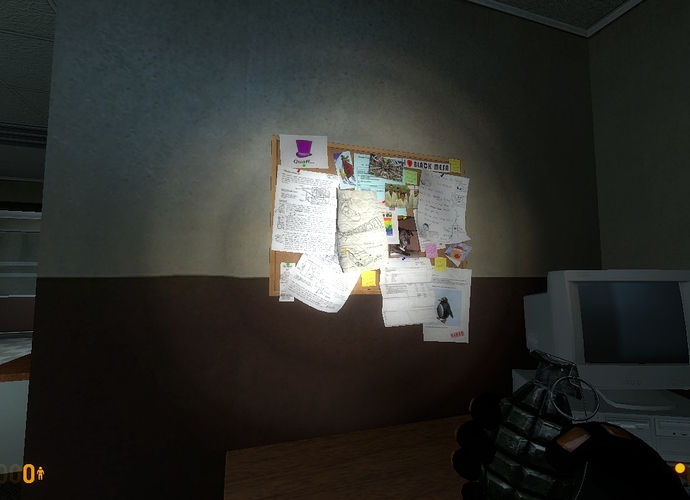
And so, we’ve come to where we are now: still no clue on how to decrypt HALOS.txt, storm’s suggestion we look in the game for more clues (but nobody has any idea where), plus not one but two confusing websites (actually… three). Although only kxbm.net currently seems to be ARG related, as localdesertsingles.com simply points to the BM website, and bmrf.us only displays the BM:Steam release video. The previously existing terminal.bmrf.us is also dead (terminal.blackmesasource.com isn’t, though!). Stormseeker recently updated his own website, and I’m not counting that as “confusing” because it seems like we have a relatively solid grasp on that, but perhaps we’re missing stuff on there as well.
“Good luck!”