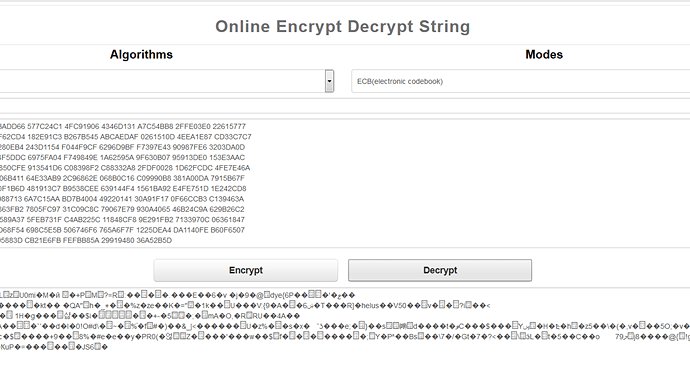
ECB mode is the simplest mode of operation that can be used with a block cipher. Other modes use a so-called initialization vector (IV) which is unknown to us. However, it is possible that the IV is part of the (hex decoded) code, for example the first or the last block could be the IV. The IV doesn’t have to be secret, and it is therefore often sent along with the encrypted data.
If Storm used a block cipher in ECB mode, then we can most likely rule out 128-bit (and larger) block ciphers, because 16 (128 bit) doesn’t evenly divide 376. This is assuming the coded data is complete and nothing is missing from the code.
On the other hand, if it is a 128-bit block cipher, then we can rule out ECB mode and we need to look at the stream cipher modes CFB, OFB and CTR.
The CTR mode is a bit different from the others in that it uses a counter which is incremented for each block. The initial counter is usually initialized with an IV like the other IV-based modes. In some cases this counter is split in half where the left half is initialized with a value called a nonce, and the right part is initialized to 0 or 1. For a 128-bit block cipher the nonce could be 8 bytes, and maybe the first 8 bytes of the code is the nonce.
Ever since the block cipher idea was suggested, the problems has always been determining the block cipher, block size, mode of operation, possible IV and key size. And then there is the question of how to transform a possible password to an actual key that can be used with the block cipher. This transformation is usually done with a key derivation function, which in the simplest form can be a simple hash function. Or, the key is simply the ASCII encoding of the password, padded or truncated to match the key length.
DES and TripleDES have an additional complication in that the key have bits that are not part of the actual key bits. These bits are called parity bits and are used for detecting simple bit errors.
One thing that has stuck out to me from 0418_08151814’s PM to Guns, is this:
I don’t know if 0418_08151814 ever mentioned 64-bit block ciphers in earlier PMs to Gunsrequiem, but it is curious that he briefly mentions the block size analysis resulting in 64 bits, but then completely omits 64-bit ciphers from his discussion and only brings up 128-bit and 256-bit block ciphers. For example:
But later, he says:
Maybe he is actually telling us exactly what we need to do here, and that we shouldn’t blindly trust everything he saying in his PM, but trust our own analysis of the code, work out the block size, modes and key lengths, and while doing so, we should probably make a few assumptions that might help narrow things down a bit, and work our way out from that.
One of the assumptions we could make is that the code is complete and isn’t missing any parts. However, there are clues that contradict this. For example, what if [ABORTIVE.] and the “data corruption” in other clues means that the code has been cut off at the end? We can still decrypt the partial message, but it means that any block size analysis is meaningless. So, we are back to square one.
We can choose to trust 0418_08151814’s suggestion that it is either 128- or 256-bit AES or Rijndael. But then in another hint we find: “Don’t trust anyone, it’s not safe.”
So, there are a lot of unknown variables that we just can’t seem to figure out or narrow down.