Its the part of office complex where a houndeye is in a room alone with a TV with static on.
First map of Office Complex chapter
Found something that is both a reference to Star Trek and “Tempus Omnia Revelat”–it seems to be a piece of fan-fiction. It was published back in 2003, and it looks like the person who wrote it resides in Britain (hence the britnurd12@yahoo.co.uk email address.) I’m not suggesting that Storm wrote it, or that the fact it was written by someone in the UK matters at all, but at this point I’ll grasp for any straws I can find. I’m at work right now, which means it’s the perfect time to read this 8o
I’ll let you guys know if anything interesting stands out.
Oh goodness. I’m glad you’re the one going through it and not me, so thank you.
I might have done a bit of skimming.
Okay, a lot. It’s mainly about Borg-human romance between Janeway and Seven. There is brief mention of a hologram that went beyond its initial bounds:
“But nothing was simple in the Delta Quadrant and just as Voyagers’ crew had learned to survive and adapt in this hostile area of space, so had this hologram. He had, over time, become a sentient being who had far surpassed what his original creators thought him capable of.”
Interesting that this is in here. I’m about 80% sure this is just a coincidence, but the previous reference to Star Trek and the title of this fan-fic nonetheless reeled me in.
Man, ARGs are a great way to garner publicity/traffic for even the most obscure entities. Perhaps I should utilize some sort of ARG/viral marketing for my website . . . .
What if the Tempus Omnia Revelant page was actually trying to send us to this fanfiction? I mean, if so that’s hilarious.
This could be very important, so i would advise you to pay attention.
In regards to the 21 goes into 1 hint that storm gave us, i might have just realized what it is.
We in the past have trowed out ideas on it, however most of them, at least to me, do not seem a very plausible.
One idea i had was that twenty-onegoesintoone, which is exactly 21 bytes long and could be a key.
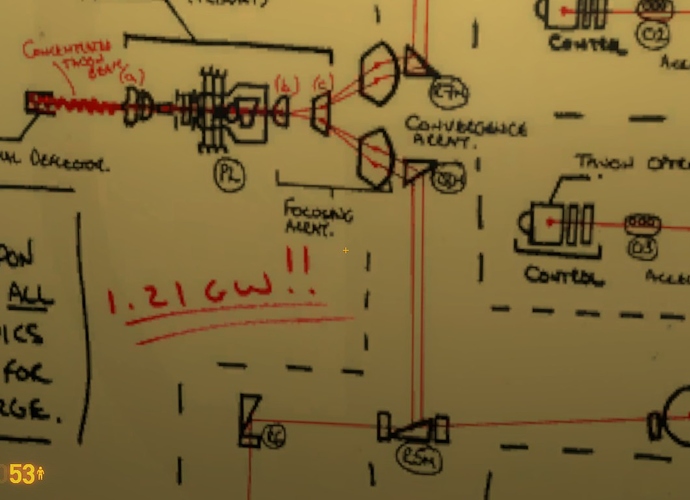
However, during my last play-through of the steam release of Black Mesa when i was in the chapter Questionable Ethics again, i looked at a whiteboard again.
The whiteboard in question was the same one with the Le Bottonamly thing on it. I will bring it up for reference. Visual representations are always needed here.
[attach=4232,none,1366][/attach]
At first this just might seem like a back to the future reference, but we human-beings can create things that have more than one use.
This could be more than a back to the future reference and something that we all have overlooked over and over again.
Notice the fact that the 1.21GW id double underlined, 21 goes into 1; .21 goes into 1.
Maybe its meant to be 1,021 instead of 1.21, well guess what, 1,021 IS PRIME.
Not only is it a prime number, but IT IS ALSO A LARGE PRIME NUMBER.
This could be a breakthrough, but this needs more time for all of us to analyze this further.
Wouldn’t it make more sense to use 1,000,000,021 instead? Since we’re dealing with the “Giga-” prefix, and that, too, is a prime number. Just a thought.
Neither of those make any sense. 1.21 scaled up gives 1,210 or 1,210,000,000, which are even numbers and therefore not prime.
1,021 is not a large prime number. Take another prime number of the same length, say 1,009. n then becomes 1,009 * 1,021 = 1,030,189, which is easily factorable. The whole point of using large prime numbers is to make the product n=p*q virtually impossible to factor using today’s computing power. So, the prime numbers have to be very large.
If the HALOS file was encrypted in one go with Benaloh, n would have to be large enough to fill 3008 bits. A number that large (< 2[sup]3008[/sup]) will have up to 906 digits, making p and q around 453 digits each.
The prime numbers could be smaller, but then the message would have to be divided into blocks. Previously, in posts here and here, I have described how this block division might cause a pattern of zeros or lower-valued numbers occurring at regular intervals in the code. And this pattern would probably be detectable, unless there is an additional layer on top that is masking this pattern.
The entropy does seem to indicate that it was designed very purposefully, which I think suggests that one encryption method was used. If you think about the previous gate puzzle in the ARG, we received the hint that “VIctor would like this extension”–although the answer was not the VIC cipher, it ended up being SECOM, an extension of VIC. Perhaps we are receiving the same sort of clue here–it’s not Benaloh or Paillier, but a derivative of them.
Furthermore, I don’t think we should exclude the Lucifer cipher. We have at least three references to it:
- Storm’s message in which he analyzes the different possibilities–a 128-bit or 256-bit encryption method were his top picks, and Lucifer uses 128 bits and was the precursor to DES.
- The LIES.jpg image in which Dr. Stone looks like Satan
- The grilledpizza.jpg image with the “when you’re building a cage for Satan” quote.
Hmm. Considering we’ve already got some biblical references, has anyone thought that the 21 into 1 hint was actually some sort of clue to a bible verse?
Regarding the Lucifer cipher: The story goes that Horst Feistel, an IBM employee who developed the Lucifer cipher along with his colleagues at IBM, wanted to call the cipher “Dataseal”. But the powers at be at IBM called it “Demonstration Cipher” instead, which got truncated to “Demon” (apparently due to file name limitations in the OS they were using at the time). Finally, the name was changed to “Lucifer” as a pun on “Demon”.
With this in mind, I think it is very possible that we may have additional references to the Lucifer cipher in the Steam release:
- The weird business going on with Dr. Sezen’s monitor, where the entity name of the monitor is “dmon”, as seen in the .vmf source file of the map.
- The comment found in one of the maps stating that the map is possessed.
With a fair warning of ‘I don’t really understand encryption well,’ but according to Benaloh’s Wiki page, it’s a derivative of the cryptosystem Goldwasser-Micali, and when I googled “goldwasser micali example” on Google, the top result is very suspicious. Note that the author of the book linked to is D. J. A. Welsh as well (although the D is for Dominic, not Dr.), which is likely to just be a big coincidence, but still funny.
EDIT: Also to note: Goldwasser-Micali could tie into Lapis Philosophorum. Maybe the Gold(which could be Goldwasser), Aqua Regia, Phlogiston, and Water are symbolic of some kind of encryption systems used to break(dissolve) this code? mean, there have been hints at HALOS being a cascade encryption.
Sorry if that doesn’t make any sense. X/
Nice, I had forgotten about those. The monitor message mentions getting ideas for “Code” from Star Trek s04e03, which someone suggested was “Brothers” from TNG. If that’s the case, I found this passage in the script:
“DATA: (imitating Picard) Computer, establish a security code for access to all functions previously transferred to Bridge.
COMPUTER: Enter code.
DATA: One seven three four six seven three two one four seven six Charlie three two seven eight nine seven seven seven six four three Tango seven three two Victor seven three one one seven eight eight eight seven three two four seven six seven eight nine seven six four three seven six. Lock.
COMPUTER: Security code intact for all specified inquiries and orders.
DATA: Computer, initiate cascade sequence, accepting instructions from Commander Data en route. (enters turbolift) Now.”
The other reference on the Tempus page: “It is one thing to communicate with something mysterious, but it is quite another to be silently observed by it. I am concerned whether it understands the same concept of reason that we do.”
This episode was about a strange entity attaching itself to Data and being able to read his mind. I know these have both been mentioned before, but they bear repeating if they spark some kind of thought. The thing is, we can know exactly what encryption method was used, but without a password we’re up shit creek.
Another thing I noticed–in the PM he sent to me, Storm mentioned rainbow attacks and bruteforcing keys perhaps being “necessary.” Well, both of these thoughts could refer to password hashing, which is required to enable the storage of passwords. If this is his method, I doubt he would salt the hashing, as that would make it nigh impossible to crack. Therefore, is it possible that the hex portion of the HALOS.txt file is simply a bunch of hashed words? The only foreseeable issue with this is that the entropy would have to be manufactured by not repeating the same word at all. That would be tough.
Well, it’s not that tough. He might have used a different capitalization for each instance of a word, e.g., pizza, Pizza, pIzza, PIzza, etc. Smaller words might pose a problem though; they would probably have to be combined with other words. However, there would be less chance of getting repeated hashes by dividing the message, not into words, but into blocks of n characters.
For example, the message “This is a message left for Dr. Horn: The Pizza is a LIE!” can be divided into eight seven-character strings:
This is
a mess
age lef
t for D
r. Horn
: The P
izza is
a LIE!
Encoding this will just be a matter of hashing each string, and joining all the hashes together to produce the code, which might be solvable using a rainbow table that covers ASCII characters 32-126 with plaintext length up to seven characters.
Storm has all but told us that the Philosopher’s Stone references are a red herring.
…Unless he didn’t.
=====
snippet
x blocks of n characters… What if n = 21? That would give meaning to “21 into 1” (i.e. 21 characters into 1 block). But how many blocks?
x blocks of n characters… What if n = 21? That would give meaning to “21 into 1” (i.e. 21 characters into 1 block). But how many blocks?
Wouldn’t work, at least not without padding.
17.9 and some change if the ASCII characters are taking up 8 bits.
20.4 and some change if they’re taking up 7.
That brings up one of the points that makes me sad–technically, ASCII characters can be encoded with 7 bits instead of 8. Are you starting to understand why we haven’t solved this, yet? Lol.
x blocks of n characters… What if n = 21? That would give meaning to “21 into 1” (i.e. 21 characters into 1 block). But how many blocks?
Wouldn’t work, at least not without padding.
17.9 and some change if the ASCII characters are taking up 8 bits.20.4 and some change if they’re taking up 7.
That brings up one of the points that makes me sad–technically, ASCII characters can be encoded with 7 bits instead of 8. Are you starting to understand why we haven’t solved this, yet? Lol.
With this idea, we are working on the assumption that the code is a sequence of hashes, where each hash is the hash of a piece of plaintext. Therefore, the number of blocks is determined by the size of the hash for the particular hash function we are looking at. With MD5 (128 bits), we get 23 hashes from the 752 hex code with 8 bytes left over. With SHA1 (160 bits) we get 18 hashes with 16 bytes left over.
In theory, the sizes of the plaintext blocks could be anything, since anything from a single character to a large file can be hashed, but we are limited to what is feasible to crack. The rainbow tables I have found on the web only covers up to 10 character plaintexts, depending on the character set being used (up to 12 characters for numeric characters only).
EDIT: But, wouldn’t this hash cracking idea be a type of problem that would be relatively easy to solve for people with the skills and resources available to them like those gentlemen from Cambridge? Just a thought.