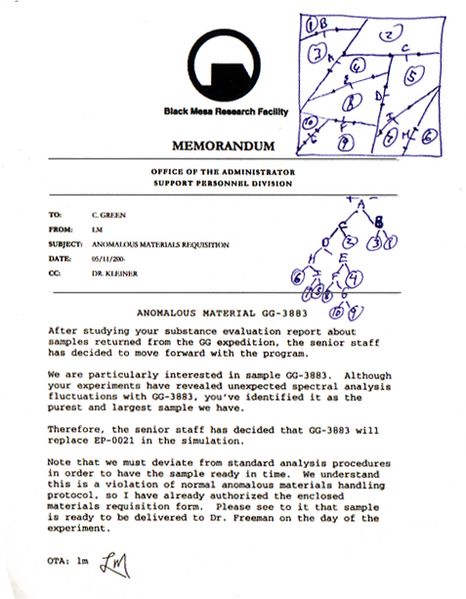
The most logical reference “the pizza is a lie” could relate to is the delivery of specimen GG-3883. It replaced specimen EP-0021 in a rush. In Half-Life 2 Eli reveals G-Man brought the sample to Black Mesa. Below is the letter sent to Colette Green from LM (Marc Laidlaw who helped develop the story-line) explaining the switch. Take note of the writings in pen, I believe they could be related to the HEX code and Pizza files on Storm’s site.
Remember the clue “21 into 1”?
The initial sample was EP-0021 and It was scheduled to go into the anti-mass spectrometer.
Could anti-mass spectrometer possibly be the key?
base64 reprents an array of bytes in readable / printable charecters, since writing it as 0010101101101 would be long
the only way for it not be valid base64 is if it contains invalid charecters 
… or if the number of characters is not multiple of 4.
But this one is correctly padded with “=” at the end.
some base64 standarts do not require the padding as mandatory
Heh just noticed something. Relating to the whole 47 thing earlier.
Niobium = 7 letters.
Who can decode this?
owFtUWtIFFEY3d0yXStL0qBYIy8iWbbM496dncVH9oCkiEw08tEyjzvrsDqzO7tu
bWpE9EAICUUo2oKUAsEeYPlAIyHNwIgEi974R/0RSRmGRkp3xP7F/XG5555zvu98
39X1qyw2a/xY4Ybzbclt1tHBb6KleCraUgdEXY4CTx3w4+VLUTUfNgKGqoWBB0Aa
cVCWJZGRoAQ5yFI8ctNIoDiZhjyluBmBoWmBAdmgSg+ZCmIjCiHsVHWCkYdXlQn6
H37t8gcNFYQUmpEUjkUQUiyN3TwlswqFWIGiKJMYwoYm1GDCjuiSEK4NgYZsQMCI
KmGzZbPyCkGsMRSnbviILGDoYV3SqwlaFQ4HPKYoHA2YrFNY9K7ovaKqySQyEUSw
EVJ1DXhowpTCqmlIQ4pz0SzLwGyATwdUA3tVk4E4l5t0R5llcMQclEtALMORI/Mc
hBi5BBclUlhkKEhysAKWJZ4XBAGLiJUljGWFTBa5Ievi3CKWgJkoqOnAg0ibgo9Y
hlSfRtIaGDQkNlodqy1Wm2VNnM3cmiXRvvHfLuemEiwXb9stmw8dCc32l+R05Onn
Zpp9hVzJ9oI8bWtRMDM1rajs1brjty5cypyd+JybGPTfNTK7q1Nb0psWRjKUGBy3
oc7Yvp7vz/N35NJS7HdS+3SjY0171v0PWQNjGc8KHl77Wlr8fqRCftG7NDTq2FvZ
4/w5PJ/gLxs+OncwrnVpoDWh88Harp2x2fTrexq/3FPc0eCjrvgU6432tLPvnE8d
dj8ab/LMjaR+vHkZNx87+WsgZ3dxPxjqm+xIs/OTSSlFdxZfy+rj1ko++UqcfdOM
ffpJ3uLb7i1NfYenygZLk37Ul/uol/v1/G0LzK76id4/Y2cqPqE3OeXzwQMnKlr+
Ag==
=wv7h
kitor:
It’s not decoding as b64. Where you found it?
Blarg. That made me find and reset my password.
People delurk over stupidest of things, I guess.It is 100% valid base64 (copypaste from the beginning to the == padding), decoding to a 673-byte binary file that doesn’t seem recognizable as anything.
That “=wv7h” part is not part of base64 - dunno, might be part of a decryption key. (The format reminds me of U.S. radio station callsigns, though!)Assuming it’s not a troll - and right now all signs point to “maybe” - one of you probably should look if this isn’t something familiar after all.
offset+hex+ascii dump:
00000000 a3 01 6d 51 6b 48 14 51 18 dd dd 32 5d 2b 4b d2 |..mQkH.Q...2]+K.| 00000010 a0 58 23 2f 22 59 b6 cc e3 de 9d 9d c5 47 f6 80 |.X#/"Y.......G..| 00000020 a4 88 4c 34 f2 d1 32 8f 3b eb b0 3a b3 3b bb 6e |..L4..2.;..:.;.n| 00000030 6d 6a 44 f4 40 08 09 45 28 da 82 94 02 c1 1e 60 |mjD.@..E(......`| 00000040 f9 40 23 21 cd c0 88 04 8b de f8 47 fd 11 49 19 |.@#!.......G..I.| 00000050 86 46 4a 77 c4 fe c5 fd 71 b9 e7 9e 73 be ef 7c |.FJw....q...s..|| 00000060 df d5 f5 ab 2c 36 6b fc 58 e1 86 f3 6d c9 6d d6 |....,6k.X...m.m.| 00000070 d1 c1 6f a2 a5 78 2a da 52 07 44 5d 8e 02 4f 1d |..o..x*.R.D]..O.| 00000080 f0 e3 e5 4b 51 35 1f 36 02 86 aa 85 81 07 40 1a |...KQ5.6......@.| 00000090 71 50 96 25 91 91 a0 04 39 c8 52 3c 72 d3 48 a0 |qP.%....9.R<r.H.| 000000a0 38 99 86 3c a5 b8 19 81 a1 69 81 01 d9 a0 4a 0f |8..<.....i....J.| 000000b0 99 0a 62 23 0a 21 ec 54 75 82 91 87 57 95 09 fa |..b#.!.Tu...W...| 000000c0 1f 7e ed f2 07 0d 15 84 14 9a 91 14 8e 45 10 52 |.~...........E.R| 000000d0 2c 8d dd 3c 25 b3 0a 85 58 81 a2 28 93 18 c2 86 |,..<%...X..(....| 000000e0 26 d4 60 c2 8e e8 92 10 ae 0d 81 86 6c 40 c0 88 |&.`.........l@..| 000000f0 2a 61 b3 65 b3 f2 0a 41 ac 31 14 a7 6e f8 88 2c |*a.e...A.1..n..,| 00000100 60 e8 61 5d d2 ab 09 5a 15 0e 07 3c a6 28 1c 0d |`.a]...Z...<.(..| 00000110 98 ac 53 58 f4 ae e8 bd a2 aa c9 24 32 11 44 b0 |..SX.......$2.D.| 00000120 11 52 75 0d 78 68 c2 94 c2 aa 69 48 43 8a 73 d1 |.Ru.xh....iHC.s.| 00000130 2c cb c0 6c 80 4f 07 54 03 7b 55 93 81 38 97 9b |,..l.O.T.{U..8..| 00000140 74 47 99 65 70 c4 1c 94 4b 40 2c c3 91 23 f3 1c |tG.ep...K@,..#..| 00000150 84 18 b9 04 17 25 52 58 64 28 48 72 b0 02 96 25 |.....%RXd(Hr...%| 00000160 9e 17 04 01 8b 88 95 25 8c 65 85 4c 16 b9 21 eb |.......%.e.L..!.| 00000170 e2 dc 22 96 80 99 28 a8 e9 c0 83 48 9b 82 8f 58 |.."...(....H...X| 00000180 86 54 9f 46 d2 1a 18 34 24 36 5a 1d ab 2d 56 9b |.T.F...4$6Z..-V.| 00000190 65 4d 9c cd dc 9a 25 d1 be f1 df 2e e7 a6 12 2c |eM....%........,| 000001a0 17 6f db 2d 9b 0f 1d 09 cd f6 97 e4 74 e4 e9 e7 |.o.-........t...| 000001b0 66 9a 7d 85 5c c9 f6 82 3c 6d 6b 51 30 33 35 ad |f.}.\...<mkQ035.| 000001c0 a8 ec d5 ba e3 b7 2e 5c ca 9c 9d f8 9c 9b 18 f4 |.......\........| 000001d0 df 35 32 bb ab 53 5b d2 9b 16 46 32 94 18 1c b7 |.52..S[...F2....| 000001e0 a1 ce d8 be 9e ef cf f3 77 e4 d2 52 ec 77 52 fb |........w..R.wR.| 000001f0 74 a3 63 4d 7b d6 fd 0f 59 03 63 19 cf 0a 1e 5e |t.cM{...Y.c....^| 00000200 fb 5a 5a fc 7e a4 42 7e d1 bb 34 34 ea d8 5b d9 |.ZZ.~.B~..44..[.| 00000210 e3 fc 39 3c 9f e0 2f 1b 3e 3a 77 30 ae 75 69 a0 |..9<../.>:w0.ui.| 00000220 35 a1 f3 c1 da ae 9d b1 d9 f4 eb 7b 1a bf dc 53 |5..........{...S| 00000230 dc d1 e0 a3 ae f8 14 eb 8d f6 b4 b3 ef 9c 4f 1d |..............O.| 00000240 76 3f 1a 6f f2 cc 8d a4 7e bc 79 19 37 1f 3b f9 |v?.o....~.y.7.;.| 00000250 6b 20 67 77 71 3f 18 ea 9b ec 48 b3 f3 93 49 29 |k gwq?....H...I)| 00000260 45 77 16 5f cb ea e3 d6 4a 3e f9 4a 9c 7d d3 8c |Ew._....J>.J.}..| 00000270 7d fa 49 de e2 db ee 2d 4d 7d 87 a7 ca 06 4b 93 |}.I....-M}....K.| 00000280 7e d4 97 fb a8 97 fb f5 fc 6d 0b cc ae fa 89 de |~........m......| 00000290 3f 63 67 2a 3e a1 37 39 e5 f3 c1 03 27 2a 5a fe |?cg*>.79....'*Z.| 000002a0 02 |.| 000002a1
This isn’t Base 64, looks like, but isn’t.
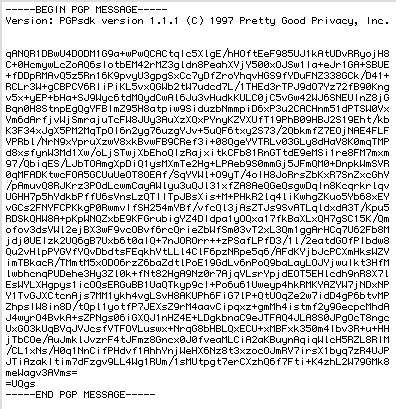
I remember once I saw a code like this so I made a little dig on the internet and I found, this is a PGP encriptation or something similar, I don’t know how to decode this, but this is a start.
Here is a exemple of a PGP mail:
edit: I expanded my search a little and looks like a SSH key too:
A exemple of a SSH-RSA key
AAAAB3NzaC1yc2EAAAABIwAAAQEAklOUpkDHrfHY17SbrmTIpNLTGK9Tjom/BWDSU
GPl+nafzlHDTYW7hdI4yZ5ew18JH4JW9jbhUFrviQzM7xlELEVf4h9lFX5QVkbPppSwg0cda3
Pbv7kOdJ/MTyBlWXFCR+HAo3FXRitBqxiX1nKhXpHAZsMciLq8V6RjsNAQwdsdMFvSlVK/7XA
t3FaoJoAsncM1Q9x5+3V0Ww68/eIFmb1zuUFljQJKprrX88XypNDvjYNby6vw/Pb0rwert/En
mZ+AW4OZPnTPI89ZPmVMLuayrD2cE86Z/il8b+gw3r3+1nKatmIkjn2so1d01QraTlMqVSsbx
NrRFi9wrf+M7Q==
If the code is a SSH key, one of the sites of the ARG should has a anormal port listening, or the 22 port.
If the code is a SSH key, one of the sites of the ARG should has a anormal port listening, or the 22 port.
I remember from a while ago when me and a bunch of chat users were working on this that I think it had something like that.
Who can decode this?
owFtUWtIFFEY3d0yXStL0qBYIy8iWbbM496dncVH9oCkiEw08tEyjzvrsDqzO7tu
bWpE9EAICUUo2oKUAsEeYPlAIyHNwIgEi974R/0RSRmGRkp3xP7F/XG5555zvu98
39X1qyw2a/xY4Ybzbclt1tHBb6KleCraUgdEXY4CTx3w4+VLUTUfNgKGqoWBB0Aa
cVCWJZGRoAQ5yFI8ctNIoDiZhjyluBmBoWmBAdmgSg+ZCmIjCiHsVHWCkYdXlQn6
H37t8gcNFYQUmpEUjkUQUiyN3TwlswqFWIGiKJMYwoYm1GDCjuiSEK4NgYZsQMCI
KmGzZbPyCkGsMRSnbviILGDoYV3SqwlaFQ4HPKYoHA2YrFNY9K7ovaKqySQyEUSw
EVJ1DXhowpTCqmlIQ4pz0SzLwGyATwdUA3tVk4E4l5t0R5llcMQclEtALMORI/Mc
hBi5BBclUlhkKEhysAKWJZ4XBAGLiJUljGWFTBa5Ievi3CKWgJkoqOnAg0ibgo9Y
hlSfRtIaGDQkNlodqy1Wm2VNnM3cmiXRvvHfLuemEiwXb9stmw8dCc32l+R05Onn
Zpp9hVzJ9oI8bWtRMDM1rajs1brjty5cypyd+JybGPTfNTK7q1Nb0psWRjKUGBy3
oc7Yvp7vz/N35NJS7HdS+3SjY0171v0PWQNjGc8KHl77Wlr8fqRCftG7NDTq2FvZ
4/w5PJ/gLxs+OncwrnVpoDWh88Harp2x2fTrexq/3FPc0eCjrvgU6432tLPvnE8d
dj8ab/LMjaR+vHkZNx87+WsgZ3dxPxjqm+xIs/OTSSlFdxZfy+rj1ko++UqcfdOM
ffpJ3uLb7i1NfYenygZLk37Ul/uol/v1/G0LzK76id4/Y2cqPqE3OeXzwQMnKlr+
Ag==
=wv7h
xchelon was right about PGP.
It’s Radix-64 encoding, which is basically base64 with a 24-bit CRC checksum (the [tt]=wv7h[/tt] thing at the end is the checksum). Radix-64 is the encoding used by PGP/OpenPGP for encoding binary data into a format known as ASCII armor (.asc file).
I ran gpg on it (after formatting and saving it as a proper ASCII armored file) and it turns out that it’s a signed PGP/OpenPGP message (compressed but not encrypted).
This is what I got:
{"body":{"key":{"fingerprint":"41574ddcb2c4c4743095815a07d1490f82a211a2","host":"keybase.io","key_id":"07d1490f82a211a2","uid":"14f55f12cf73544031e890d3f053a000","username":"vocatus"},"service":{"hostname":"bmrf.org","protocol":"http:"},"type":"web_service_binding","version":1},"ctime":1407613324,"expire_in":157680000,"prev":"46a5327272d9744e56a60b0eb204a003aedc99aaaeb53dceedf5745843678bec","seqno":5,"tag":"signature"}which led me to this:
and
Note that it’s bmrf.org and not bmrf.us.
The file at https://bmrf.org/keybase.txt
[spoiler][code]==================================================================
https://keybase.io/vocatus
I hereby claim:
- I am an admin of https://bmrf.org
- I am vocatus (https://keybase.io/vocatus) on keybase.
- I have a public key with fingerprint 4157 4DDC B2C4 C474 3095 815A 07D1 490F 82A2 11A2
To claim this, I am signing this object:
{
“body”: {
“key”: {
“fingerprint”: “41574ddcb2c4c4743095815a07d1490f82a211a2”,
“host”: “keybase.io”,
“key_id”: “07d1490f82a211a2”,
“uid”: “14f55f12cf73544031e890d3f053a000”,
“username”: “vocatus”
},
“service”: {
“hostname”: “bmrf.org”,
“protocol”: “http:”
},
“type”: “web_service_binding”,
“version”: 1
},
“ctime”: 1407613324,
“expire_in”: 157680000,
“prev”: “46a5327272d9744e56a60b0eb204a003aedc99aaaeb53dceedf5745843678bec”,
“seqno”: 5,
“tag”: “signature”
}
with the aforementioned key, yielding the PGP signature:
-----BEGIN PGP MESSAGE-----
Version: GnuPG v1
owFtUWtIFFEY3d0yXStL0qBYIy8iWbbM496dncVH9oCkiEw08tEyjzvrsDqzO7tu
bWpE9EAICUUo2oKUAsEeYPlAIyHNwIgEi974R/0RSRmGRkp3xP7F/XG5555zvu98
39X1qyw2a/xY4Ybzbclt1tHBb6KleCraUgdEXY4CTx3w4+VLUTUfNgKGqoWBB0Aa
cVCWJZGRoAQ5yFI8ctNIoDiZhjyluBmBoWmBAdmgSg+ZCmIjCiHsVHWCkYdXlQn6
H37t8gcNFYQUmpEUjkUQUiyN3TwlswqFWIGiKJMYwoYm1GDCjuiSEK4NgYZsQMCI
KmGzZbPyCkGsMRSnbviILGDoYV3SqwlaFQ4HPKYoHA2YrFNY9K7ovaKqySQyEUSw
EVJ1DXhowpTCqmlIQ4pz0SzLwGyATwdUA3tVk4E4l5t0R5llcMQclEtALMORI/Mc
hBi5BBclUlhkKEhysAKWJZ4XBAGLiJUljGWFTBa5Ievi3CKWgJkoqOnAg0ibgo9Y
hlSfRtIaGDQkNlodqy1Wm2VNnM3cmiXRvvHfLuemEiwXb9stmw8dCc32l+R05Onn
Zpp9hVzJ9oI8bWtRMDM1rajs1brjty5cypyd+JybGPTfNTK7q1Nb0psWRjKUGBy3
oc7Yvp7vz/N35NJS7HdS+3SjY0171v0PWQNjGc8KHl77Wlr8fqRCftG7NDTq2FvZ
4/w5PJ/gLxs+OncwrnVpoDWh88Harp2x2fTrexq/3FPc0eCjrvgU6432tLPvnE8d
dj8ab/LMjaR+vHkZNx87+WsgZ3dxPxjqm+xIs/OTSSlFdxZfy+rj1ko++UqcfdOM
ffpJ3uLb7i1NfYenygZLk37Ul/uol/v1/G0LzK76id4/Y2cqPqE3OeXzwQMnKlr+
Ag==
=wv7h
-----END PGP MESSAGE-----
And finally, I am proving ownership of this host by posting or
appending to this document.
View my publicly-auditable identity here: https://keybase.io/vocatus
==================================================================
[/code][/spoiler]
… contains the same signed PGP message that SupaSoldier posted.
So, apparently this guy, who goes by the name of Vocatus Gate, owns the domain bmrf.org, and is using Keybase and the signed keybase.txt file on the bmrf.org site to prove it.
Domain Name:BMRF.ORG
Domain ID: D173238236-LROR
Creation Date: 2014-07-07T22:03:18Z
Updated Date: 2014-09-06T03:47:11Z
Registry Expiry Date: 2015-07-07T22:03:18Z
Sponsoring Registrar:NetEarth One Inc. d/b/a NetEarth (R1902-LROR)
Sponsoring Registrar IANA ID: 1005
WHOIS Server:
Referral URL:
Domain Status: clientTransferProhibited – https://www.icann.org/epp#clientTransferProhibited
Registrant IDI_37446465
Registrant Name:Vocatus Gate
Registrant Organization:Black Mesa Research Facility
Registrant Street: 321 BMRF Ct
Registrant City:Black Mesa
Registrant State/Province:NV
Registrant Postal Code:89040
Registrant Country:US
Registrant Phone:+1.9281110044
Registrant Phone Ext:
Registrant Fax:
Registrant Fax Ext:
Registrant Email:
Admin IDI_37446465
Admin Name:Vocatus Gate
Admin Organization:Black Mesa Research Facility
Admin Street: 321 BMRF Ct
Admin City:Black Mesa
Admin State/Province:NV
Admin Postal Code:89040
Admin Country:US
Admin Phone:+1.9281110044
Admin Phone Ext:
Admin Fax:
Admin Fax Ext:
Admin Email:
Tech IDI_37446465
Tech Name:Vocatus Gate
Tech Organization:Black Mesa Research Facility
Tech Street: 321 BMRF Ct
Tech City:Black Mesa
Tech State/Province:NV
Tech Postal Code:89040
Tech Country:US
Tech Phone:+1.9281110044
Tech Phone Ext:
Tech Fax:
Tech Fax Ext:
Tech Email:
Name Server:NS1.SGC-HOSTING.COM
Name Server:NS2.SGC-HOSTING.COM
Name ServerNS1.SGC-HOSTING.COM
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
DNSSEC:Unsigned
Interesting contact info…
I don’t think that this has anything to do with the ARG, though.
Heh just noticed something. Relating to the whole 47 thing earlier.
Niobium = 7 letters.
Here’s something I noticed some time ago, but then completely forgot about it:
The digit sum of Dr Horn’s number 1001085139140914 is 47, and the number of distinct digits is 7.
I thought you didn’t now about it, but I’ve seen now flavrans9 post about how it’s not ARG related.
I thought you didn’t now about it, but I’ve seen now flavrans9 post about how it’s not ARG related.
Lol. I found it two weeks ago, but i was thinking that is not ARG related and i posted just a PGP message
Here’s something I noticed some time ago, but then completely forgot about it:
The digit sum of Dr Horn’s number 1001085139140914 is 47, and the number of distinct digits is 7.
so the password for the hex file is just 1001085139140914
bmrf now redirects to https://www.kxbm.net/article/?view=all-clear-given-for-black-mesa-evacuation-zone-10360
any other url for that domain will bring you to an error screen video using the same EAS_bg image, but overlaid with increasingly heavy distortion and occasional flashes of the G-Man.
interesting things found;
two interesting scripts from the error page. maybe nothing or nothing special but they stand out for obvious reasons. first one because, well;
https://kxbm.net/assets/three.min.js
the second one because it is just right in the source, and pretty weird looking;
****ing too long to post! gah! anyway it looks like it might be encoded ascii art (maybe the familiar lambda ascii art logo)? you’ll see it at the bottom of the source page.


There is an email address for the ‘author’ of the article Tim Evans, tim@kxbm.net
The domain “kxbm.net” was just registered on the 15th of this month.
If you click on the follow on twitter link at the new BMFR site there is this link https://www.localdesertsingles.com, when i checked it there was some stuff inside if you inspect the element with firefox. Also here is the twitter site that shows a link to the BMFR site https://twitter.com/time_van
Here’s something I noticed some time ago, but then completely forgot about it:
The digit sum of Dr Horn’s number 1001085139140914 is 47, and the number of distinct digits is 7.
so the password for the hex file is just 1001085139140914
The 47 thing came up a few times already, its also a number on a calculator in the QE level, and a few other things, its a link to the number 42, as 47 is 42 accounting for inflation.
Also if 1001085139140914 was the code for the Hex file, then its either to long or to short, if you remove the 0’s you get 8 digits though
Also note that the amount of the comments on the site is 22 which could do something with the 22 in to 1 clue.
And when at the bottom of the article it reads 12 twitter retweets but when you click to show them it goes to the twitter page and says there are no retweets of it
Except for the fact that the clue was 21 into 1