Perhaps–maybe he was trying to pull more people in to help us?
I know I said I was going to take some time away from this, but I just keep feeling like we’re right on the cusp of solving this and one solid push in the right direction would take us where we need to go.
I was reviewing (for about the 100,000th time) the messages that Code/Storm sent me, and something about this still bothers me:
"
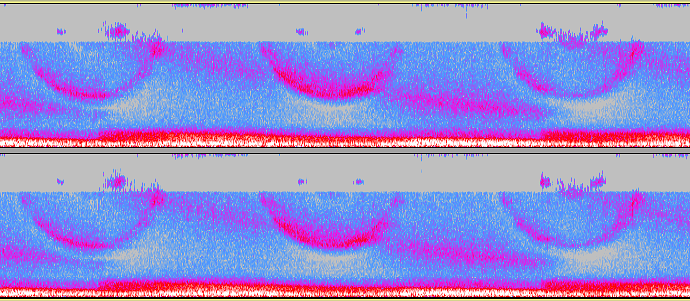
I ran the code through a few programs that analyze entropy via auto-correlation, the n gram results indicate a weak encryption, but one that results in highly entropic data (which I correlated against a similar data set size from a randomness extractor) when decoded via Hex, which I suspect is a secondary encode, as most encrypted data sent via communications is encoded in order to avoid corruption. This may have skewed the block size analysis done previously (resulting in 376bytes or 64bits).
Source Code[/size]
- ³+�:5ºÝfW|$ÁOÉCFÑ1§ÅK¸/þà"aWw?$y#Ü!ö,Ô.‘ògµE«Êí¯aQ
- Nê‡Í3ÇÇ?q10œÄ(´$=TðDùÏb–Ù¿÷9~C˜æ2Ú
- ?äx³¥O]Üiuú÷I„žbYZŸc•‘=à>:¬?8ŒEû…þ‘5AÖÀƒ˜òȃ2¨/ß�(büÜOçäj?éQÅÈ´dã:¹,–†.‹À™¸8�Úy¶?ä¢Y›mHǹSŒîc‘Dôaº’äþu$,Ø?QÖ•Q˜‡j|ª½{@I"A0©f̳Á9F:?~š7ª†?²xü—1ÀœŒy~y“
- @eF²Lšb›&Â?Î*KäXš7_ësÄ«"\„Œøž)²q3—6G?J‰(íÖTiŒ^[PgFövZo%Þ¤Ú@þ¶e?E$i6•ˆ=Ë!æûþû¸Z)‘”€6¥+]
"
First and foremost, he considered this the source code, and even mentions that the hex encoding was simply another layer added on to prevent corruption. With that in mind, it would actually be this ASCII representation that we would need to look at. Another thing that bugs me about this is how the code is broken up into lines. Why? Does that indicate individual sentences? I’ve copy/pasted it myself, and it does break into these lines automatically.
Therefore, if this is the actual source code (he even labeled it as such), then what encryption methods do we know of that create standardized and extended ASCII characters?
I also recall running the decimal form of the ASCII characters through the CryptoCrack program, and it returned just a few points off (4, to be exact) the tridigital cipher. I have a brief description of how it works on the blog–unfortunately, trying to solve it in CryptoCrack terminates the program with an error message.